It’s been an exciting decade for cryptography; as a result we see smaller key sizes and weaker algorithms getting deprecated.
One driver of such things is the U.S. Federal Government, specifically NIST.
One example of this would be NIST Special Publication 800-131A which disallows the use of SHA1 after December 2013. What this means is if you are in the U.S. Federal Government or you work with them you may have to revise your technology strategy to use SHA2 in its place.
But what if you don’t have any policy mandate forcing you to do this switch? Well it’s a good idea but it has consequences too, namely compatibility.
You see SHA2 was published in 2001 so anything produced before then will not support it. The most notable example is Windows XP which as of July 2012 has about 29% presence on the Internet.
This is important for more than just Internet Explorer users since even Chrome and Safari use CryptoAPI for certificate validation when on Windows.
The good news is that XP SP3 which was released in 2008 added support for this new suite of hash algorithms, that begs the question how many of those XP machines have XP SP3?
Unfortunately I don’t have any public references that can answer this question but let’s that 85% of all XP machines on the Internet have gotten this update (I have good confidence in this number) that means that 15% of those 29% would not be able to connect to your server over SSL if you used SHA2.
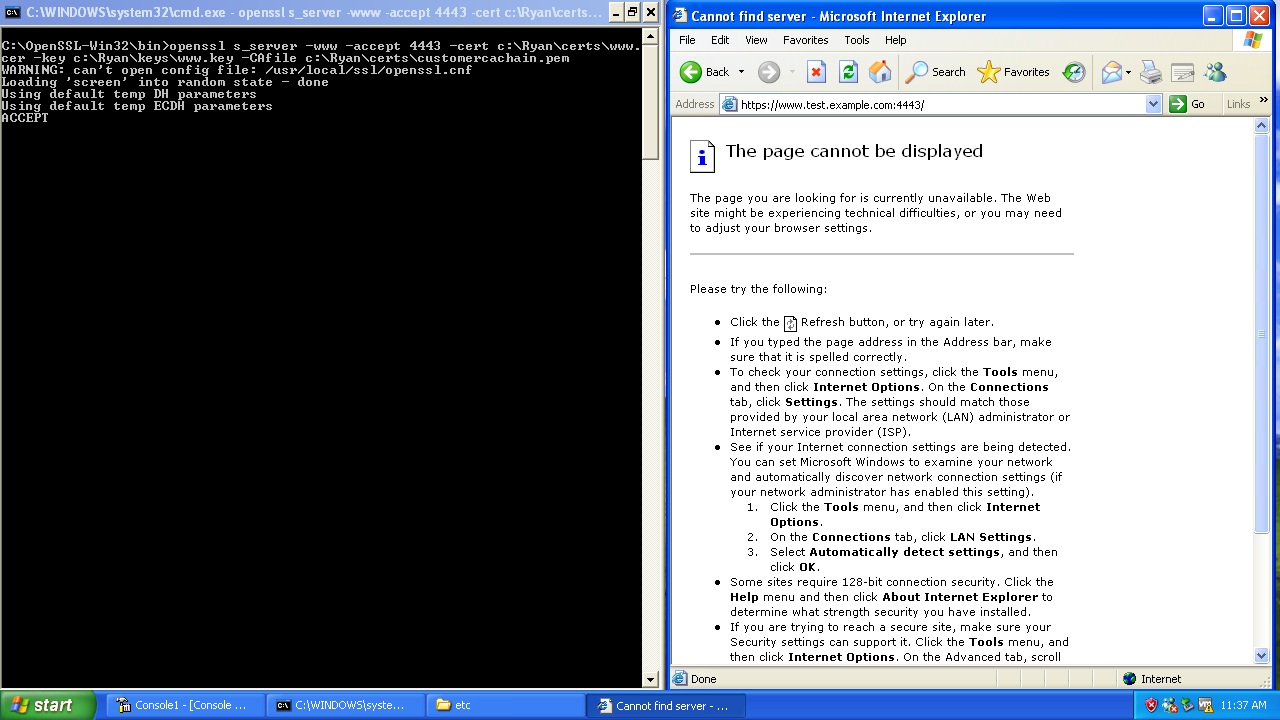
This would mean these users would see something like this:
That is pretty scary, so how long until we can use this more broadly? It’s hard to say there is a good article titled “The developers guide to browser adoption rates” that sheds some light, that and the historic gs.statcounter.com results. Based on these unless there is a sudden change (which is possible these machines are getting pretty old) I would assume that we have around 4-5 years of XP out there yet.
Hope this helps,
Ryan
MS stopped supporting XP/SP2 two years ago (ref: http://windows.microsoft.com/en-us/windows/products/lifecycle). At some point the cord to the past needs to be cut to push the rest of the world forward (how long are we going to keep letting security decisions be determined by people who are using an incredibly old and out-of-date OS?)
Do you believe that now is an acceptable time to cut XP/SP2 support in TLS? If not now, when?
Michael, its sad I know. That said this works out to not being able to communicate to 6% oft he hosts on the internet – Many businesses cant consider such a decision. The SHA2 problem is less interesting than the ECC one, that’s around 29% of the hosts that can’t do it and it would provide real immediate value today — unfortunately XP again keeps us from deploying it. I think we still have 4 years of this lowest common denominator problem to contend with.
I’m toying with the idea of a tweet-based key distribution mechanism, making use of the small size of ECC keys.
Given your interest, could one conclude that your employer will roll out an ECC chain at some point?
Remember that Windows only supports NIST P192 to P521. And the performance difference isnt huge between the smallest curve supported and the next one up – http://www.nsa.gov/business/programs/elliptic_curve.shtml. As for GlobalSIgn, we already issue ECC certificates just off our existing chains. We also have pure ECC chains but they are not super ubiquitous at this time. Give it another year and they will be sufficiently iniquitous for many usages.
Don’t forget Server 2003 that ends support in July 2015. I doubt there are many browsing using it outside of terminal servers, but for those users, they would have to ask the admin to install the hotfix (KB968730), which would require a reboot.
Chrome bug on this: http://code.google.com/p/chromium/issues/detail?id=109400